Today’s discovery is not a big deal too, just another Clickjacking in the world, but this time in the newly added “OPT-IN” feature by coinhive and authedmine but first let’s know some terms before we begin.
What is Coinhive?
Coinhive is a cryptocurrency mining service that relies on a small chunk of javascript code designed to be installed on Web sites.
What is Clickjacking?
Clickjacking, also known as a “UI redress attack”, is when an attacker uses multiple transparent or opaque layers to trick a user into clicking on a button or link on another page when they were intending to click on the the top level page. Thus, the attacker is “hijacking” clicks meant for their page and routing them to another page, most likely owned by another application, domain, or both.
Using a similar technique, keystrokes can also be hijacked. With a carefully crafted combination of stylesheets, iframes, and text boxes, a user can be led to believe they are typing in the password to their email or bank account, but are instead typing into an invisible frame controlled by the attacker.
What is CryptoJacking?
CryptoJacking, Also known as cryptocurrency mining, it refers to the fact that your system’s resources are being utilised to mine virtual currencies without your consent. This is possible by using a javascript code on the website, which when visited by you, starts the mining process.
Hackers have been able to hack websites to run such scripts. But at the same time, there are websites, who are using plug-and-play scripts from services like Coinhive.com.
In a nutshell, both hackers or some popular websites you visit (such as Piratebay) can use your device to mine cryptocurrencies.
Using a similar technique, keystrokes can also be hijacked. With a carefully crafted combination of stylesheets, iframes, and text boxes, a user can be led to believe they are typing in the password to their email or bank account, but are instead typing into an invisible frame controlled by the attacker.
The Discovery
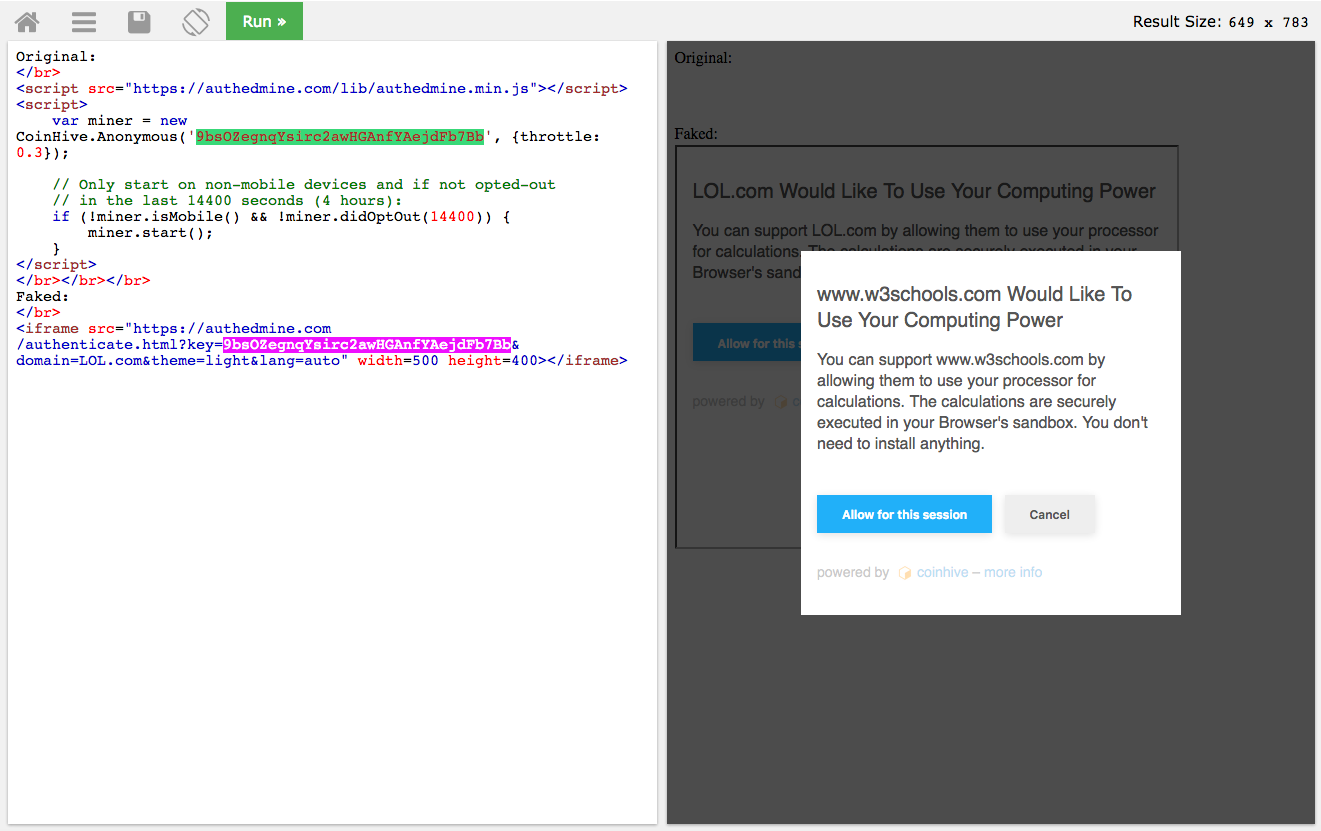
During our closer look to the new implementation of Coinhive’s new “OPT-IN” feature to remedy the bad reputation it got by misusing their service by cyber criminals we found that the javascript code responsible of including the miner inside the website is neither checking the window size it loads it
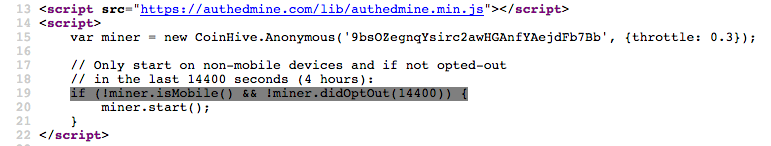
nor where is it being actually hosted, that means a website called “X” can host the miner code/opt-in feature iframe of the website called “Y” hence the user could be tricked into clicking on it.
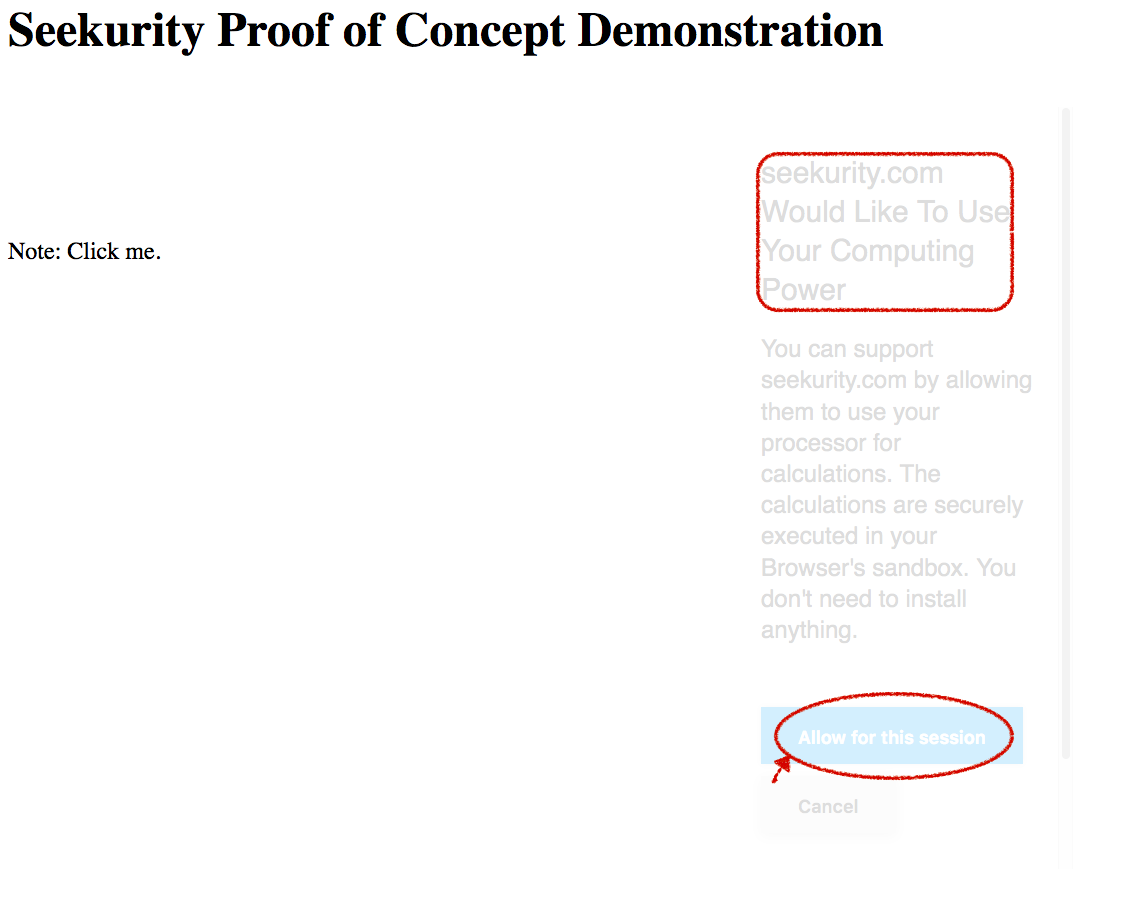
Proof of concept video:
Attack Vectors:
– Website owners will trick their visitors into click on any visible element where the real mouse click goes to a hidden coinhive’s authedmine iframe to click on.
How to protect yourself?
- Install a specialized browsers extensions/addons like (NoMiner, minerBlock, AdBlock Plus) and this is a useful article about blocking cryptomining (https://seekurity.com/services/goto/3x).
- Security awareness, try to learn about everything for your awareness to avoid being a victim to the latest bypasses and attacks that can harm you.
- Monitor your computer/device processes and if you noticed a strange behavior (eg. CPU is going high or your machine temperature becomes hot periodically).
[-] Disclaimer:
Any advisories and discoveries by Seekurity SAS de C.V. is subject to Seekurity SAS de C.V. responsible disclosure rules which is a 15-90-day-disclosure-deadline or NON-Responsive vendor after that if no response or a patch has been made broadly available, the bug details will become visible to the public through our official communication channels.
A minute if you please!
Building a website, an application or any kind of business? Or already have one? Worried about your security? Think twice before going public and let us protect your business!
"feature" and Bypassing ClickJacking Coinhive cryptocurrency CryptoJacking machines mine monero OPT-IN optin their to trick user Users via

Previous Next